With Oracle Sites Cloud Services, access to any site is Public, by default. If you have to add authentication, there is a very simple way to achieve it:
First, we assume that authentication will be against the existing Identity Domain provided with the tenant.
In a dedicated page of a site, called Login for instance, we add an App component which embeds an URL to any folder of Documents Cloud Service.
ie:
App URL =
https://documents.XX.oraclecloud.com/documents/embed/home/nameasc
Note that the URL will be called with the EMBED keyword.
Then we add the App component is a region, and we setup a height=1 and a width=1 (almost invisible).
That's all.
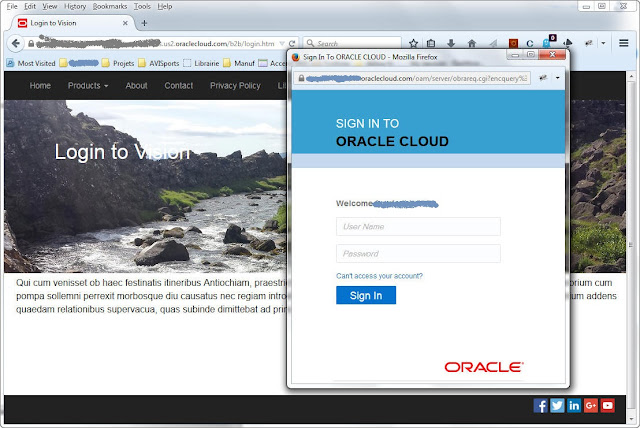
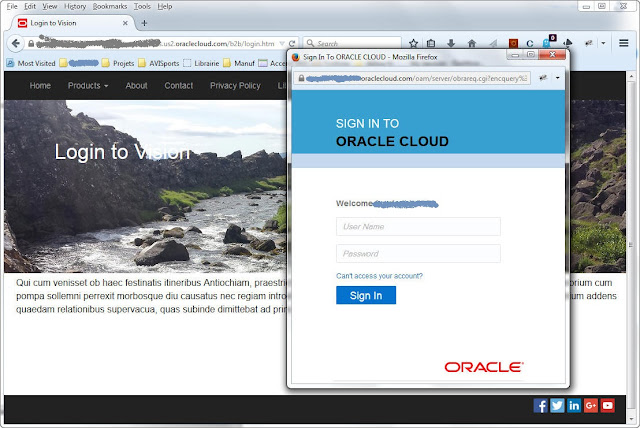
Each time a user will navigate to this custom Login Page, and if the user is not yet authenticated, a new page will splash on the screen, asking for credentials. Once login and pasword are provided by the user, the page disapears and return to custom Login page.
Optionnaly it's possible to add a dedicated button which triggers a logout by adding this link:
https://myservices.us2.oraclecloud.com/mycloud/faces/adfAuthentication?
logout=true&end_url=https://documents.sites.us2.oraclecloud.com//
Prerequisites: Authorize Documents Cloud Service to embed Folder in an iframe and add the domain to the granted list. (In Administration menu)
Other advantages: If you have a subscription to Database Service in the same Identity Domain, the method described above will be a good way to introduce an authentication to an APEX component.
Cf my other post related to Apps.
First, we assume that authentication will be against the existing Identity Domain provided with the tenant.
In a dedicated page of a site, called Login for instance, we add an App component which embeds an URL to any folder of Documents Cloud Service.
ie:
App URL =
https://documents.XX.oraclecloud.com/documents/embed/home/nameasc
Note that the URL will be called with the EMBED keyword.
Then we add the App component is a region, and we setup a height=1 and a width=1 (almost invisible).
That's all.
Each time a user will navigate to this custom Login Page, and if the user is not yet authenticated, a new page will splash on the screen, asking for credentials. Once login and pasword are provided by the user, the page disapears and return to custom Login page.
Optionnaly it's possible to add a dedicated button which triggers a logout by adding this link:
https://myservices.us2.oraclecloud.com/mycloud/faces/adfAuthentication?
logout=true&end_url=https://documents
Prerequisites: Authorize Documents Cloud Service to embed Folder in an iframe and add the domain to the granted list. (In Administration menu)
Other advantages: If you have a subscription to Database Service in the same Identity Domain, the method described above will be a good way to introduce an authentication to an APEX component.
Cf my other post related to Apps.
Commentaires